OAuth 2.0: Difference between revisions
| Line 44: | Line 44: | ||
===Types=== | ===Types=== | ||
There are five Grant Types | There are five Grant Types | ||
*Authorization Code Grant Type | *Authorization Code Grant Type () | ||
*Implicit Grant Type | *Implicit Grant Type | ||
*Resource Owner Credentials Grant Type | *Resource Owner Credentials Grant Type | ||
Revision as of 11:18, 18 July 2021
Introduction
History
Previously we used
- XML
- SOAP
- SAML or WS-*
Now we Use
- JSON
- HTTP APIs
- OAuth and OpenID Connect
Credential Sharing
Previously we used to use credential Sharing. E.g. Problems with this are
- We can impersonate the use
- Issues around revocation
- Exposed user credentials
Cookies
Next solution was cookies but CSRF and XSRF attacks were common.
API Key
Next API Key, this works well accept for where the app has no backend. E.g. Single Page App.
- API Keys have no standard
- Expiration management
OAuth 2.0
Features include
- Authorization framework
- Built for HTTP APIs
- Scoped access (User defined what can be used)
- Delegation Protocol
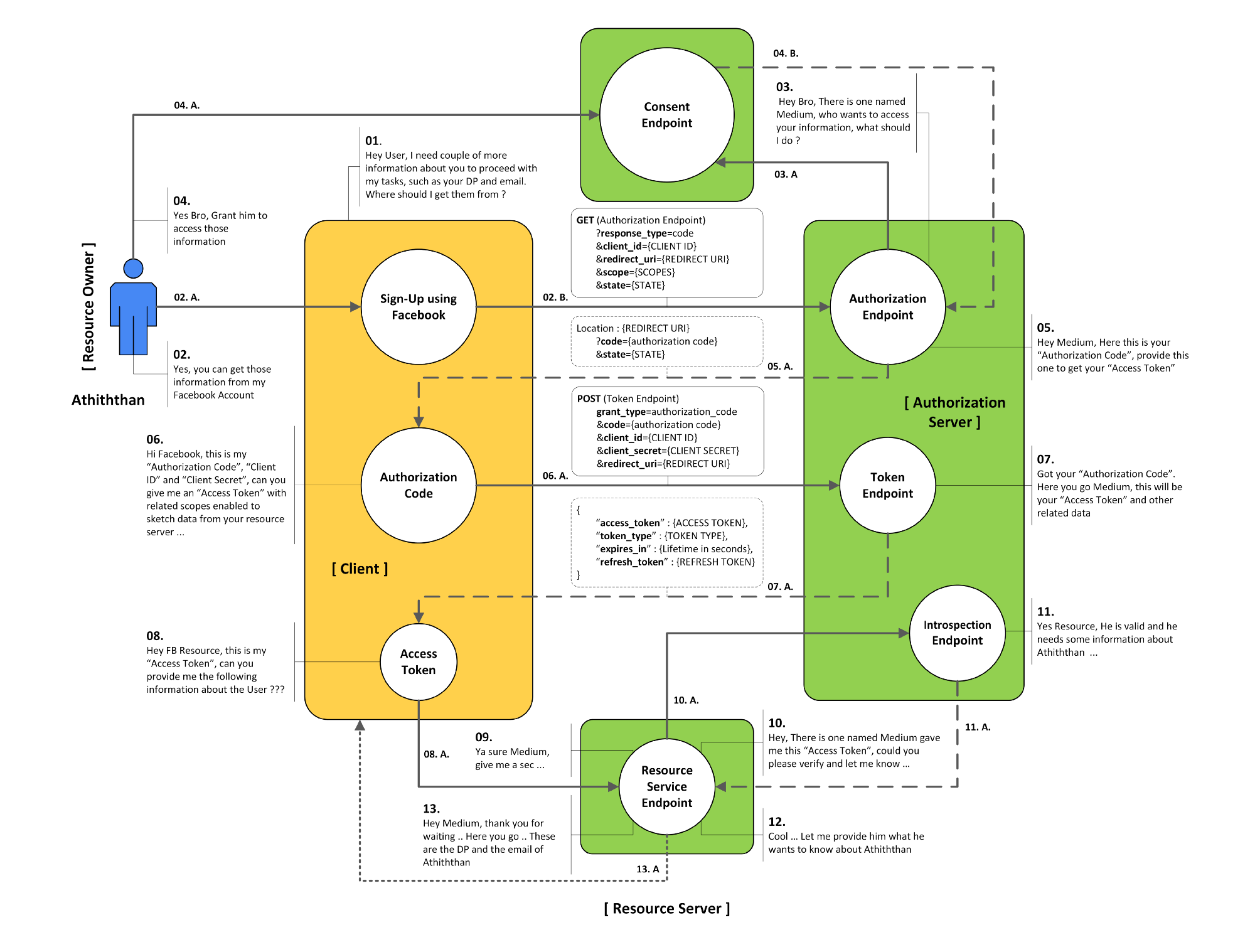
Players include
- Protected Resource (Our API)
- Client (requesting application)
- Resource Owner (the user)
- Authorization Server
Here is the flow for OAuth 2.0
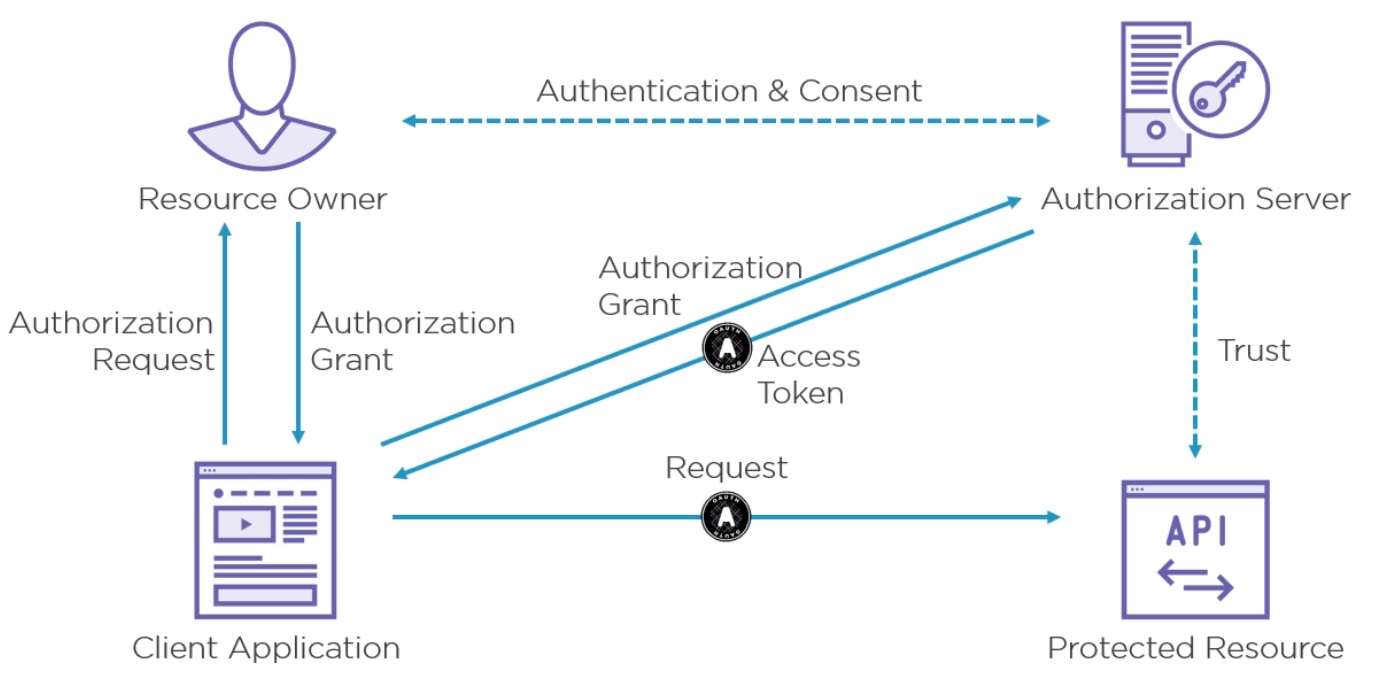
How the API trusts the access token is out of scope for OAuth but if is up to the Protected Resource to do this before sending the response.
Detail
Endpoints
The Protocol endpoint are either
- Authorization Handles all user interaction by the user agent
- Token - This endpoint is for machines only
Scope
A scope in OAuth is a permission to do something with a protected resource. E.g. access to API, Read/Write, Feature.
Grant Types
Types
There are five Grant Types
- Authorization Code Grant Type ()
- Implicit Grant Type
- Resource Owner Credentials Grant Type
- Client Credentials Grant Type
- Refresh Token Grant
Full Authorization Code Grant Type Flow
The Authorization Code Grant Type is the most commonly used grant type to authorize the Client to access protected data from a Resource Server.